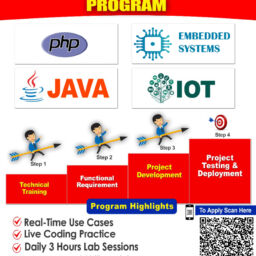
we are published title for the academic year 2015-2016. we are deals with java, j2ee, dot.net, ns2, matlab simulation, ieee power system and power electronics simulation and hardware projects, embedded, plc and vlsi projects. ieee projects in pondicherry
|
S.NO |
TITLE |
CODE |
DOWNLOAD |
|
KNOWLEDGE AND DATA ENGINEERING / DATA MINING |
|||
| 1 | Efficient Filtering Algorithms for Location-Aware Publish/Subscribe | LM_J015_01 | ABSTRACT |
| 2 | Probabilistic Range Query over Uncertain Moving Objects in Constrained Two-Dimensional Space | LM_J015_02 | ABSTRACT |
| 3 | CrowdOp: Query Optimization for Declarative Crowdsourcing Systems | LM_J015_03 | ABSTRACT |
| 4 | Disease Inference from Health-Related Questions via Sparse Deep Learning | LM_J015_04 | ABSTRACT |
| 5 | Real-Time City-Scale Taxi Ridesharing | LM_J015_05 | ABSTRACT |
| 6 | t-Closeness through Microaggregation: Strict Privacy with Enhanced Utility Preservation | LM_J015_06 | ABSTRACT |
|
PARALLEL DISTRIBUTED SYSTEM |
|||
| 7 | A Proximity-aware Interest-clustered P2P File Sharing System | LM_J015_07 | ABSTRACT |
| 8 | Neighbor Similarity Trust against Sybil Attack in P2P E-Commerce | LM_J015_08 | ABSTRACT |
| 9 | Secure and Verifiable Policy Update Outsourcing for Big Data Access Control in the Cloud | LM_J015_09 | ABSTRACT |
| 10 | Neighbor Discovery in Wireless Networks with Multipacket Reception | LM_J015_10 | ABSTRACT |
| 11 | Truthful Greedy Mechanisms for Dynamic Virtual Machine Provisioning and Allocation in Clouds | LM_J015_11 | ABSTRACT |
| 12 | VMbuddies: Coordinating Live Migration of Multi-Tier Applications in Cloud Environments | LM_J015_12 | ABSTRACT |
| 13 | A Hybrid Cloud Approach for Secure Authorized Deduplication | LM_J015_13 | ABSTRACT |
| 14 | Secure and Distributed Data Discovery and Dissemination in Wireless Sensor Networks | LM_J015_14 | ABSTRACT |
|
Dependable and Secure Computing |
|||
| 15 | Anonymous Two-Factor Authentication in Distributed Systems: Certain Goals Are Beyond Attainment | LM_J015_15 | ABSTRACT |
| 16 | A Lightweight Secure Scheme for Detecting Provenance Forgery and Packet Drop Attacks in Wireless Sensor Networks | LM_J015_16 | ABSTRACT |
| 17 | Secure Data Aggregation Technique for Wireless Sensor Networks in the Presence of Collusion Attacks | LM_J015_17 | ABSTRACT |
| 18 | Secure Spatial Top-k Query Processing via Untrusted Location-Based Service Providers | LM_J015_18 | ABSTRACT |
| 19 | Key-Recovery Attacks on KIDS, a Keyed Anomaly Detection System | LM_J015_19 | ABSTRACT |
|
NETWORKING |
|||
| 20 | Path Reconstruction in Dynamic Wireless Sensor Networks Using Compressive Sensing | LM_J015_20 | ABSTRACT |
|
COMPUTERS |
|||
| 21 | Maximizing P2P File Access Availability in Mobile Ad Hoc Networks though Replication for Efficient File Sharing | LM_J015_21 | ABSTRACT |
| 22 | Key-Aggregate Searchable Encryption (KASE) for Group Data Sharing via Cloud Storage | LM_J015_22 | ABSTRACT |
| 23 | Cost-Effective Authentic and Anonymous Data Sharing with Forward Security | LM_J015_23 | ABSTRACT |
|
MOBILE COMPUTING |
|||
| 24 | Privacy-Preserving and Truthful Detection of Packet Dropping Attacks in Wireless Ad Hoc Networks | LM_J015_24 | ABSTRACT |
| 25 | Tracking Message Spread in Mobile Delay Tolerant Networks | LM_J015_25 | ABSTRACT |
| 26 | Tracking Message Spread in Mobile Delay Tolerant Networks | LM_J015_26 | ABSTRACT |
| 27 | Dynamic Routing for Data Integrity and Delay Differentiated Services in Wireless Sensor Networks | LM_J015_27 | ABSTRACT |
| 28 | Privacy-Preserving Ciphertext Multi-Sharing Control for Big Data Storage | LM_J015_28 | ABSTRACT |
|
INFORMATION FORENSICS AND SECURITY |
|||
| 29 | Privacy-Preserving Ciphertext Multi-Sharing Control for Big Data Storage | LM_J015_29 | ABSTRACT |
| 30 | Privacy-Control Cloud Data Access Privilege and Anonymity With Fully Anonymous Attribute-Based Encryption | ||
we are offering ieee projects, ns2 projects, android project, final year projects for ME/MTECH,BE/BTECh,MCA/MSCStudents. we are offering java/j2ee projects, dotnet projects,ns2 projects and ieee project